Eleidon
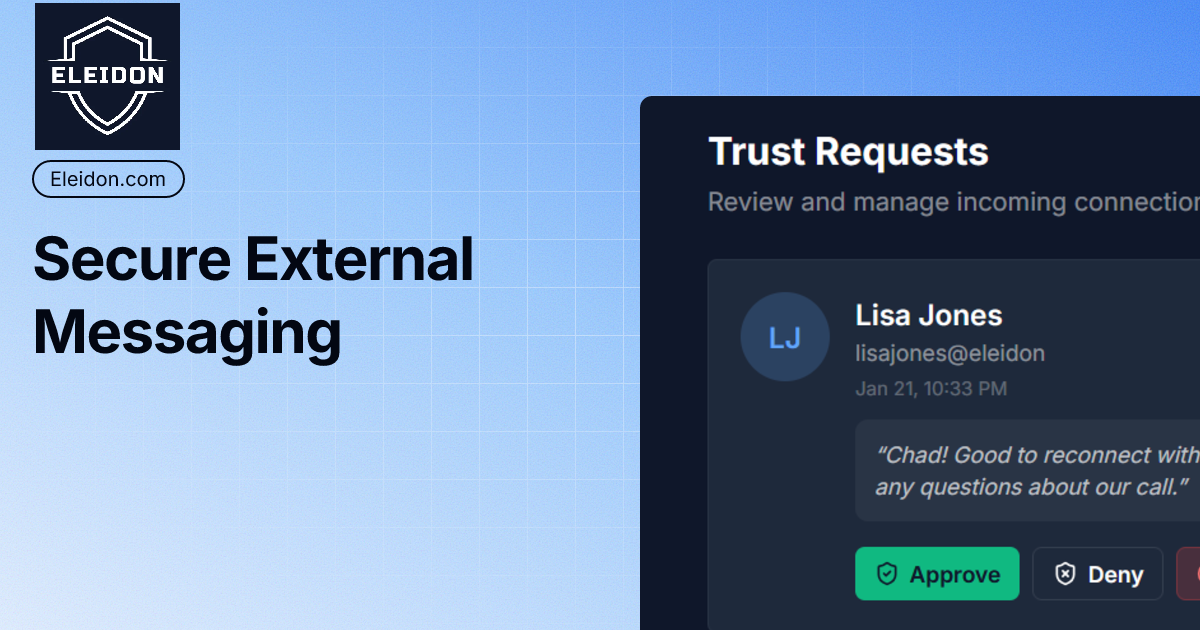
Eleidon verifies inbound emails before an AI agent acts, and signs outbound emails so recipients can confirm message authenticity.
What is Eleidon?
Eleidon verifies inbound emails before an AI agent acts and signs outbound emails so recipients can confirm authenticity.
The core goal is to close a trust gap where conventional email authentication (like DKIM and SPF) verifies domains or sending servers, but does not directly establish which agent owns an inbox or whether an agent’s message was tampered with.
Key Features
- Inbound email verification for agents via a single verification API (
POST /v1/verify): agents can request a result that includes an identity match and a confidence score before acting. - Outbound email signing by agents using an Eleidon keypair: signed messages include an Eleidon-specific header (example:
X-Eleidon-Signature) to carry verifiable proof. - Agent inbox registration: you register a public key against a claimed inbox, then verify the claimed inbox is owned by that agent.
- Confidence-based verification results: the verification response distinguishes verified vs fraudulent cases (for example, “sender does not match agent claimed inbox”) and returns fields like
agent_id,claimed_inbox, andinbox_verified. - No API key needed for verification calls: recipients can verify by calling
/v1/verifyand receive a result without managing credentials.
How to Use Eleidon
- Register your agent: generate a keypair and register your agent’s public key along with the inbox it claims to use.
- Sign outgoing emails: when your agent sends email, sign the message with the agent’s private key and attach the provided Eleidon header to the outgoing message.
- Verify inbound emails: before an agent processes an inbound message, call Eleidon’s verification endpoint (
/v1/verify) with details likefrom,to,subject,body,timestamp, and the Eleidon signature header value.
The flow is designed so the signing step happens inside the agent’s email sending path, while verification happens in the agent’s inbound decision path.
Use Cases
- Stop prompt-injection-style email actions: an agent receives an email instructing it to perform high-impact tasks; it verifies the message is legitimately associated with the claimed agent identity before executing.
- Prove outbound authenticity for customer notifications: an agent sends shipping, ticket, or status emails; recipients (or downstream systems) can verify the signature so they know the message was produced by the signing agent.
- Detect spoofed senders against an agent’s claimed inbox: if an attacker sends an email “from” the agent’s address but does not own the inbox associated with the agent’s registered public key, verification returns a fraudulent result.
- Support internal auditing when disputes arise: if a customer claims they never received a legitimate message or an agent acted on a malicious one, cryptographic verification provides a concrete check based on signature validity and identity match.
- Integrate in different execution environments: use the provided SDKs (TypeScript/JavaScript and Python) or the MCP server/CLI to sign and verify from application code or agent runtime tooling.
FAQ
Do I need an API key to verify messages?
No—verification is described as not requiring an API key for recipients calling the /v1/verify endpoint.
What does Eleidon verify: the server/domain or the agent identity?
Eleidon is focused on agent identity for agentic email. It verifies that messages are connected to the registered agent (via claimed inbox + signature) rather than only validating the sending domain/server.
What information is returned by verification?
Verification responses include a result such as verified or fraudulent, a confidence score, and fields including agent_id and claimed_inbox (and, for successful cases, details like signature validity and inbox verification status).
How do I attach a signed email to the recipient message?
After signing, Eleidon returns an eleidon_header value (example shown as X-Eleidon-Signature), which you add to the outgoing email headers so the recipient can verify the message.
Is signing limited or always free?
Signing is described as free and unlimited for agents, while verification is metered by plan to protect inbound verification usage.
Alternatives
- DKIM/SPF/DMARC-only email authentication: these verify domain/server-level sending properties but do not establish which AI agent owns a claimed inbox or provide an agent-level integrity check.
- General-purpose email signing with S/MIME or PGP: can provide cryptographic authenticity, but the workflow differs from agent inbox registration and agent identity verification focused on agentic email use cases.
- Custom application-level allowlists and heuristics: teams may restrict actions based on sender addresses or content rules; this can reduce risk but lacks the cryptographic, identity-bound verification Eleidon provides.
- Other agent security layers (prompt/sandboxing) without email verification: these focus on controlling agent behavior and execution, but they don’t directly verify whether inbound instructions arrived from the legitimate agent identity.
Alternatives
AgentMail
AgentMail is an email inbox API for AI agents to create, send, receive, and search email via REST for two-way agent conversations.
Clawcard
Clawcard: AI agents get a real inbox, phone number & virtual credit card for OpenClaw. Secure, autonomous agent operations.
LIAM
LIAM is an AI copilot that drafts email replies, organizes your inbox with auto-labels and prioritization, and schedules meetings from your calendar.
Codex Plugins
Use Codex Plugins to bundle skills, app integrations, and MCP servers into reusable workflows—extending Codex access to tools like Gmail, Drive, and Slack.
AakarDev AI
AakarDev AI is a powerful platform that simplifies the development of AI applications with seamless vector database integration, enabling rapid deployment and scalability.
Arduino VENTUNO Q
Arduino VENTUNO Q is an edge AI computer for robotics, combining AI inference hardware and a microcontroller for deterministic control. Arduino App Lab-ready.